Navigating the 5 Phases of Ethical Hacking
In today’s digital age, cybersecurity is more critical than ever. Ethical hacking, or penetration testing, is a proactive approach to identifying vulnerabilities in systems and networks before malicious hackers can exploit them. Let’s explore the five phases of ethical hacking, each vital for ensuring a robust security posture.
If you want to excel in this career path, then it is recommended that you upgrade your skills and knowledge regularly with the latest Ethical Hacking Course in Bangalore.

1. Planning and Reconnaissance
The first phase of ethical hacking is all about preparation and information gathering. This stage involves two key activities:
- Passive Reconnaissance: Collecting publicly available information about the target, such as domain names, IP addresses, and organizational structure. This does not involve direct interaction with the target.
- Active Reconnaissance: Engaging with the target’s systems to gather more detailed information, such as scanning for open ports and services.
The goal here is to gather as much data as possible to identify potential vulnerabilities.
2. Scanning
Once gathering information is complete, the next phase is scanning. This involves using various tools to analyze the target’s network and systems. The primary activities in this phase include:
- Network Scanning: Identifying active devices and their status on the network.
- Port Scanning: Checking which ports are open and what services are running on those ports.
- Vulnerability Scanning: Utilizing automated tools to discover known security issues within the systems.
This phase helps ethical hackers develop a clearer understanding of the target’s security landscape.
3. Gaining Access
In this phase, ethical hackers attempt to exploit the identified vulnerabilities to gain unauthorized access to the system. Techniques used may include:
- Exploiting Known Vulnerabilities: Launching attacks that target specific weaknesses in software or hardware.
- Social Engineering: Manipulating individuals into leaking sensitive information, such as passwords.
The objective is to demonstrate how an attacker could breach the system and access sensitive data.
With the aid of Ethical Hacking Online Training programs, which offer comprehensive training and job placement support to anyone looking to develop their talents, it’s easier to learn this tool and advance your career.
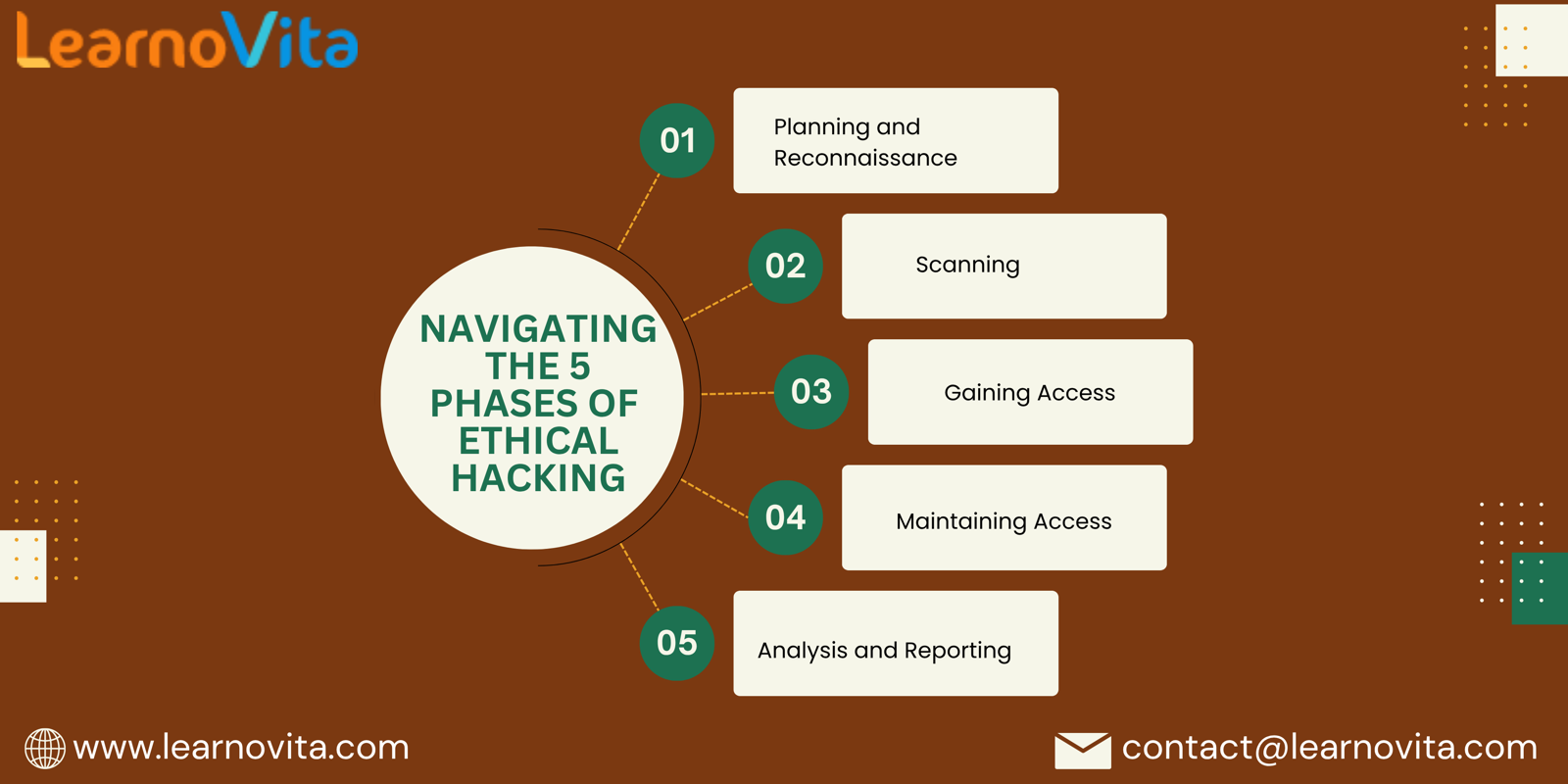
4. Maintaining Access
After successfully breaching a system, the next step is to establish a foothold within it. This phase involves:
- Creating Backdoors: Implementing tools that allow continued access to the system even after the initial vulnerability is patched.
- Privilege Escalation: Seeking higher access levels to gain further control over the system.
This phase illustrates the potential risks of an undetected breach, emphasizing the need for continuous monitoring.
5. Analysis and Reporting
The final phase is critical for translating findings into actionable insights. During this phase, ethical hackers compile a comprehensive report that includes:
- Summary of Findings: A detailed overview of all vulnerabilities discovered during the assessment.
- Recommendations: Suggested remediation strategies to address the identified issues.
- Risk Assessment: Evaluating the potential impact of each vulnerability on the organization.
This report serves as a roadmap for improving security measures and preventing future attacks.
Conclusion
Ethical hacking is an essential component of a proactive cybersecurity strategy. By following these five phases—planning and reconnaissance, scanning, gaining access, maintaining access, and analysis and reporting—organizations can effectively identify and mitigate vulnerabilities. Embracing ethical hacking not only protects sensitive information but also strengthens overall security in an increasingly complex digital landscape.
- Art
- Causes
- Crafts
- Dance
- Drinks
- Film
- Fitness
- Food
- Spellen
- Gardening
- Health
- Home
- Literature
- Music
- Networking
- Other
- Party
- Religion
- Shopping
- Sports
- Theater
- Wellness



